At ValidExamDumps, we consistently monitor updates to the Juniper JN0-664 exam questions by Juniper. Whenever our team identifies changes in the exam questions,exam objectives, exam focus areas or in exam requirements, We immediately update our exam questions for both PDF and online practice exams. This commitment ensures our customers always have access to the most current and accurate questions. By preparing with these actual questions, our customers can successfully pass the Juniper Service Provider Routing and Switching, Professional Exam exam on their first attempt without needing additional materials or study guides.
Other certification materials providers often include outdated or removed questions by Juniper in their Juniper JN0-664 exam. These outdated questions lead to customers failing their Juniper Service Provider Routing and Switching, Professional Exam exam. In contrast, we ensure our questions bank includes only precise and up-to-date questions, guaranteeing their presence in your actual exam. Our main priority is your success in the Juniper JN0-664 exam, not profiting from selling obsolete exam questions in PDF or Online Practice Test.
Exhibit
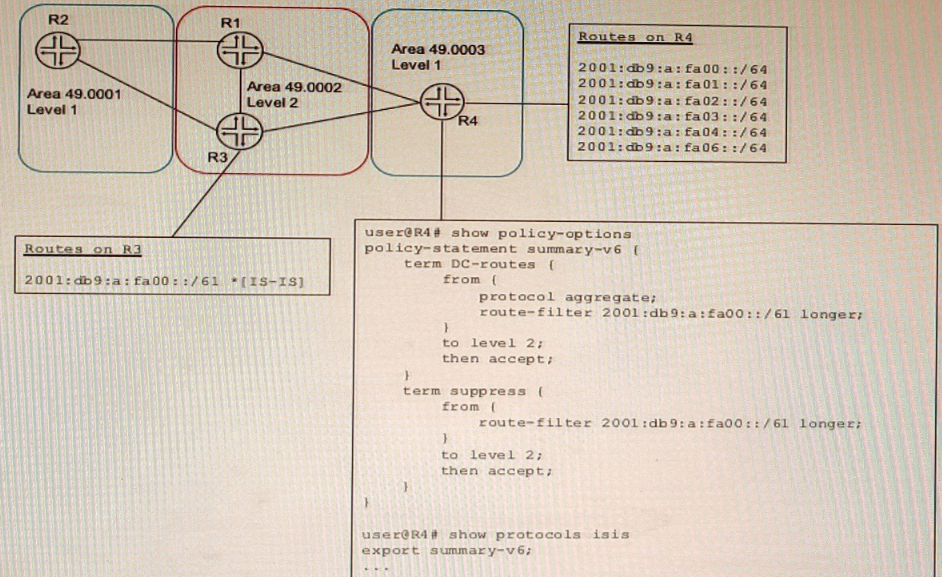
A network designer would like to create a summary route as shown in the exhibit, but the configuration is not working.
Which three configuration changes will create a summary route? (Choose three.)
To create a summary route for IS-IS, you need to configure a policy statement that matches the prefixes to be summarized and sets the next-hop to discard. You also need to configure a summary-address statement under the IS-IS protocol hierarchy that references the policy statement. In this case, the policy statement leak-v6 is trying to match the prefix 2001:db9:a:fa00::/61 exactly, but this prefix is not advertised by any router in the network. Therefore, no summary route is created. To fix this, you need to delete the longer keyword from the route-filter term and change the prefix length to /61 exact. This will match any prefix that falls within the /61 range. You also need to delete the export statement under protocols isis, because this will export all routes that match the policy statement to other IS-IS routers, which is not desired for a summary route.
Exhibit
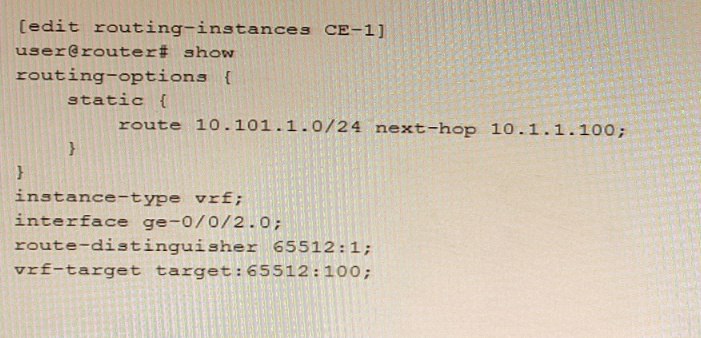
Referring to the exhibit, which statement is true?
The auto-export parameter is a routing option that allows a routing instance to share routes with other routing instances or the master routing table. The auto-export parameter automatically exports routes from one routing instance to another based on the route target communities attached to the routes. In this scenario, the 10.101.1.0/24 route will be shared if the auto-export parameter is configured under [edit routing-options] hierarchy level.
Exhibit
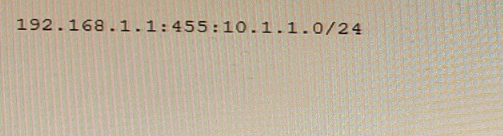
You are examining an L3VPN route that includes the information shown in the exhibit
Which statement is correct in this scenario?
Type 1: When Type value is 1, the Administrator field is 4-bytes and Assigned Number field is 2-bytes. The Administrator field should be set to the IP address (public IP addresses should be used). The Assigned Number field contains a number from a numbering space that is administered by the enterprise to which the IP address has been assigned by the appropriate authority.
Which two statements are correct regarding the PIM DR in a PIM-SM domain? (Choose two.)
In PIM-SM (Protocol Independent Multicast - Sparse Mode), the Designated Router (DR) plays a crucial role in multicast forwarding. The DR is responsible for various tasks depending on whether it is connected to the source or the receiver. Let's analyze each statement regarding the PIM DR in a PIM-SM domain.
1. **Statement A: The source DR sends PIM register messages from the source network to the RP.**
- Correct. In PIM-SM, the DR on the source's local network is responsible for encapsulating multicast packets in PIM Register messages and sending them to the Rendezvous Point (RP). This process ensures that the RP is aware of active sources.
2. **Statement B: If the DR priorities match, the router with the lowest IP address is selected as the DR.**
- Incorrect. The correct rule is that if the DR priorities match, the router with the **highest** IP address is selected as the DR. The election process first compares priorities; if priorities are equal, the IP addresses are compared to select the DR.
3. **Statement C: The receiver DR sends PIM join and PIM prune messages from the receiver network toward the RP.**
- Correct. In PIM-SM, the DR on the receiver's local network sends PIM Join messages toward the RP to join the multicast distribution tree. Similarly, it sends PIM Prune messages to leave the tree when there are no interested receivers.
4. **Statement D: By default, PIM DR election is performed on point-to-point links.**
- Incorrect. By default, PIM DR election is performed on multi-access networks (e.g., Ethernet). On point-to-point links, there is no need for a DR election as there are only two routers involved.
**Conclusion**:
The correct statements regarding the PIM DR in a PIM-SM domain are:
**A. The source DR sends PIM register messages from the source network to the RP.**
**C. The receiver DR sends PIM join and PIM prune messages from the receiver network toward the RP.**
**Reference**:
- Juniper Networks Documentation on PIM-SM: [PIM-SM Overview](https://www.juniper.net/documentation/en_US/junos/topics/concept/pim-sparse-mode-overview.html)
- RFC 7761, Protocol Independent Multicast - Sparse Mode (PIM-SM): [RFC 7761](https://tools.ietf.org/html/rfc7761) which details the PIM-SM protocol, including DR roles and election procedures.
You must alter class-of-service values in packets on the outbound interface of an edge router.
In this scenario, which CoS component allows you to accomplish this task?
Class of Service (CoS) in networking is used to manage traffic by classifying, scheduling, and sometimes modifying packets to ensure network performance and Quality of Service (QoS). Different CoS components are used to achieve these goals. Let's analyze each option to determine which CoS component allows you to alter class-of-service values on the outbound interface of an edge router.
1. **Output Policer**:
- Policing is used to control the rate of traffic sent to or from a network interface. It can drop or remark traffic that exceeds a certain rate.
- Policing is not typically used to alter CoS values but to enforce traffic limits.
2. **Scheduler**:
- A scheduler is responsible for managing the order in which packets are transmitted out of an interface based on their CoS markings. It can allocate bandwidth and prioritize traffic.
- The scheduler manages how packets are queued and sent but does not alter the CoS values of packets.
3. **Rewrite Rules**:
- Rewrite rules are used to modify the CoS values of packets, such as DSCP (Differentiated Services Code Point) or 802.1p bits, as they exit an interface.
- Rewrite rules can alter the class-of-service values in the packet headers to match the desired policies of the outbound interface.
- Therefore, rewrite rules are the correct component for altering CoS values on an outbound interface.
4. **Forwarding Classes**:
- Forwarding classes are used to categorize packets into different traffic classes within a router for QoS handling.
- They help in defining how packets should be treated by the scheduler but do not directly modify the CoS values.
**Conclusion**:
To alter class-of-service values in packets on the outbound interface of an edge router, the correct CoS component to use is:
**C. rewrite rules**
**Reference**:
- Juniper Networks Documentation on CoS: [Class of Service Overview](https://www.juniper.net/documentation/en_US/junos/topics/concept/class-of-service-overview.html)
- Junos OS CoS Configuration Guide: [Rewrite Rules](https://www.juniper.net/documentation/en_US/junos/topics/topic-map/class-of-service-rewrite-rules.html)