At ValidExamDumps, we consistently monitor updates to the Juniper JN0-1332 exam questions by Juniper. Whenever our team identifies changes in the exam questions,exam objectives, exam focus areas or in exam requirements, We immediately update our exam questions for both PDF and online practice exams. This commitment ensures our customers always have access to the most current and accurate questions. By preparing with these actual questions, our customers can successfully pass the Juniper Security Design, Specialist Exam exam on their first attempt without needing additional materials or study guides.
Other certification materials providers often include outdated or removed questions by Juniper in their Juniper JN0-1332 exam. These outdated questions lead to customers failing their Juniper Security Design, Specialist Exam exam. In contrast, we ensure our questions bank includes only precise and up-to-date questions, guaranteeing their presence in your actual exam. Our main priority is your success in the Juniper JN0-1332 exam, not profiting from selling obsolete exam questions in PDF or Online Practice Test.
You are asked to segment the networks connected to an SRX Series device into distinct logical groups with different security requirements.
How would you accomplish this task?
You are asked to perform a risk assessment for a core layer switch in your data center. After analyze the Annual loss Expectancy (ALE) for this switch, you conclude that the risk remediation strategy involves purchasing insurance to protect against losses due to compromise or failure.
This scenario describes which risk remediation strategy?
Exhibit.
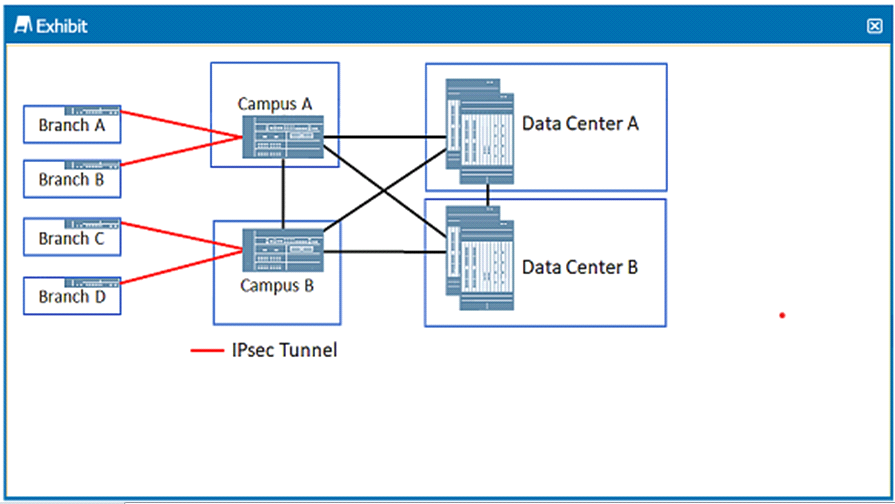
In the 3-tier VPN design shown in the exhibit, which function are the Campus A and Campus B SRX Series devices performing?
Refer to the Exhibit.
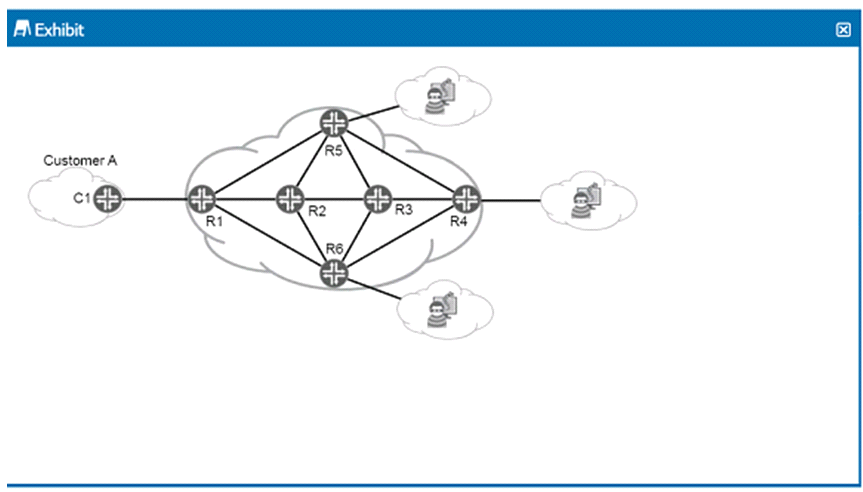
You are asked to provide a proposal for security elements in the service provider network shown in the exhibit. You must provide DOoS protection for Customer A from potential upstream attackers.
Which statements correct in this scenario?
You are asked to deploy multiple kiosk locations around the country. Their locations will change frequently and will need to access services in the corporate data center as well as other kiosk locations You need a central key location In this scenario, which solution would you deploy?