At ValidExamDumps, we consistently monitor updates to the Huawei H12-721 exam questions by Huawei. Whenever our team identifies changes in the exam questions,exam objectives, exam focus areas or in exam requirements, We immediately update our exam questions for both PDF and online practice exams. This commitment ensures our customers always have access to the most current and accurate questions. By preparing with these actual questions, our customers can successfully pass the Huawei HCIP-Security-CISN V3.0 exam on their first attempt without needing additional materials or study guides.
Other certification materials providers often include outdated or removed questions by Huawei in their Huawei H12-721 exam. These outdated questions lead to customers failing their Huawei HCIP-Security-CISN V3.0 exam. In contrast, we ensure our questions bank includes only precise and up-to-date questions, guaranteeing their presence in your actual exam. Our main priority is your success in the Huawei H12-721 exam, not profiting from selling obsolete exam questions in PDF or Online Practice Test.
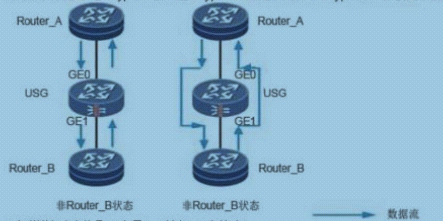
The figure shows the data flow direction of the Bypass interface in the Bypass working mode and the non-Bypass working mode. What are the following statements about the working flow of the electrical Bypass interface?
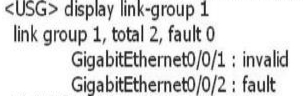
After the link-group is configured on the device, use the display link-group 1 command to obtain the following information. What information can I get?
Huawei's abnormal traffic cleaning solution must deploy an independent testing center.
Virtual firewall virtualizes multiple logical firewalls on a physical firewall device and implements multiple instances?
Note: Virtual firewalls are a combination of VPN instances (Instances), instances of multiple instances, and configuration of multiple instances. The virtual firewall provides the following multiple instances: one is VPN multi-instance; the other is secure multi-instance; the third is to configure multiple instances; the fourth is NAT multi-instance; the fifth is routing multi-instance; the sixth is UTM multi-instance.
The firewall device defends against the SYN Flood attack by using the technology of source legality verification. The device receives the SYN packet and sends the SYN-ACK probe packet to the source IP address host in the SYN packet. If the host exists, it will Which message is sent?