The H12-711_V4.0 exam validates your expertise in network security fundamentals as part of the Huawei Certified ICT Associate (HCIA) Security certification path. This assessment is designed for IT professionals who implement and support security solutions using Huawei technologies. This page provides a clear roadmap of exam topics, question formats, and actionable preparation strategies to help you build confidence and demonstrate your security knowledge effectively.
Use this topic map to guide your study for Huawei H12-711_V4.0 (HCIA-Security V4.0) within the Huawei Certified ICT Associate, HCIA Security path.
The H12-711_V4.0 exam combines knowledge-based and scenario-driven questions to assess both conceptual understanding and practical decision-making in security contexts.
Questions progress in difficulty, requiring candidates to connect multiple concepts and apply knowledge to unfamiliar situations that reflect actual network security operations.
Effective preparation combines structured topic review with hands-on practice and timed assessments. Allocate study time proportionally to exam weight, and regularly test yourself to identify gaps early.
Explore other Huawei certifications: view all Huawei exams.
Strengthen your preparation with up-to-date resources from validexamdumps.com. These materials align to H12-711_V4.0 and cover practical scenarios with clear explanations.
Visit the exam page to download the PDF, Online Practice Test, or get a bundle discount for both formats: HCIA-Security V4.0.
Firewall security policies, threat prevention, and encryption technologies typically represent the largest portion of exam questions. These domains directly reflect real-world security operations and decision-making. Allocate study time accordingly, but ensure you have foundational knowledge across all ten topics to handle integrated scenarios.
In a typical deployment, firewall policies define which traffic is allowed or blocked, NAT technologies hide internal IP addresses and manage port forwarding, and hot standby ensures the firewall remains active if the primary device fails. Understanding how these three work together, rather than in isolation, is critical for scenario-based questions and real-world security design.
Hands-on experience significantly boosts confidence and retention. Prioritize labs that cover firewall policy creation, NAT configuration, and basic IPS rule setup. If you lack access to hardware, use Huawei's virtual lab environments or simulators to practice policy syntax and rule evaluation. Even simulated practice reinforces the concepts tested on the exam.
Candidates often confuse symmetric and asymmetric encryption, misunderstand the difference between firewall policies and IPS rules, or fail to recognize when PKI certificates are required in a scenario. Another frequent error is overlooking the practical implications of NAT, for example, not realizing that NAT can block certain protocols or complicate VPN tunnels. Careful scenario reading and linking concepts to real deployments prevent these mistakes.
In your final week, focus on timed practice tests and review of incorrect answers rather than re-reading study materials. Identify patterns in your weak areas (e.g., certificate management or threat classification) and target those topics with focused Q&A sets. On the day before the exam, do a light review of key definitions and take a short, untimed practice quiz to stay sharp without overloading your memory.
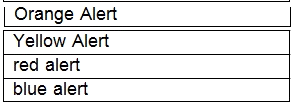
Which of the following zones is not the firewall default security zone?
Drag the warning level of the network security emergency response on the left into the box on the right, and arrange it from top to bottom in order of severity.[fill in the blank]*
When using passive mode to establish an FTP connection, the control channel uses port 20 and the data channel uses port 21. ( )[Multiple choice]*