At ValidExamDumps, we consistently monitor updates to the HPE6-A68 exam questions by HP. Whenever our team identifies changes in the exam questions,exam objectives, exam focus areas or in exam requirements, We immediately update our exam questions for both PDF and online practice exams. This commitment ensures our customers always have access to the most current and accurate questions. By preparing with these actual questions, our customers can successfully pass the HP Aruba Certified Clearpass Professional 6.7 exam on their first attempt without needing additional materials or study guides.
Other certification materials providers often include outdated or removed questions by HP in their HPE6-A68 exam. These outdated questions lead to customers failing their HP Aruba Certified Clearpass Professional 6.7 exam. In contrast, we ensure our questions bank includes only precise and up-to-date questions, guaranteeing their presence in your actual exam. Our main priority is your success in the HPE6-A68 exam, not profiting from selling obsolete exam questions in PDF or Online Practice Test.
Refer to the exhibit.
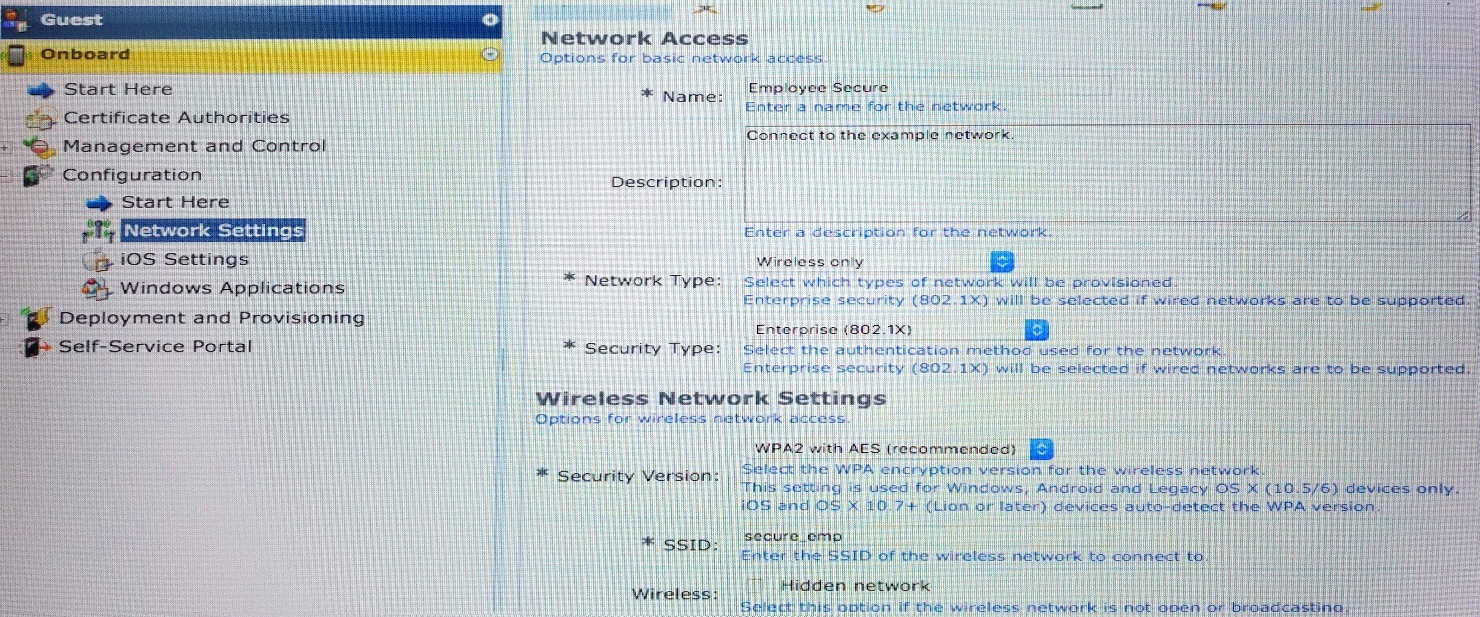
Which statements accurately describe the status of the Onboarded devices in the configuration for the network settings shown? (Select two.)
A ClearPass administrator wants to make Enforcement decisions during 802.1x authentication based on a client's Onguard posture token.
Which Enforcement profile should be used on the health check service?
The Health Check Service requires a profile to terminate the session so that the RADIUS 802.1X authentication Service can use the posture token in a new authentication routine. The terminate session profile will utilize the Change of Authorization feature to force a re-authentication.
See step 6) below.
Navigate to the list of Enforcement Profiles by selecting, Configuration > Enforcement > Profiles.
2. Click the + Add link in the upper right hand corner.
3. From the Template dropdown menu, choose RADIUS Change of Authorization (CoA).
4. Name the policy.
This example uses Dell Terminate Session as the profile name.
5. Leave all the other settings as default, and click Next > to move to the Attributes tab.
6. On the dropdown menu for Select RADIUS CoA Template, choose IETF-Terminate-Session-IETF.
7. Click Next > and review the Summary tab (Figure 22).
8. Click Save.
Campus Networks Configuring ClearPass OnGuard, Switching, and Wireless (v1.0) (September 2015), page 22
A bank would like to deploy ClearPass Guest with web login authentication so that their customers can selfregister on the network to get network access when they have meetings with bank employees. However, they're concerned about security.
What is true? (Choose three.)
A customer wants to implement Virtual IP redundancy, such that in case of a ClearPass server outage, 802.1x authentications will not be interrupted. The administrator has enabled a single Virtual IP address on two ClearPass servers.
Which statements accurately describe next steps? (Select two.)
In an Aruba network, APs are controlled by a controller. The APs tunnel all data to the controller for processing, including encryption/decryption and bridging/forwarding data. Local controller redundancy provides APs with failover to a backup controller if a controller becomes unavailable. Local controller redundancy is provided by running VRRP between a pair of controllers. The APs are then configured to connect to the ''virtual-IP'' configured for the VRRP instance.
In which ways can ClearPass derive client roles during policy service processing? (Select two.)