At ValidExamDumps, we consistently monitor updates to the Fortinet NSE5_FAZ-7.0 exam questions by Fortinet. Whenever our team identifies changes in the exam questions,exam objectives, exam focus areas or in exam requirements, We immediately update our exam questions for both PDF and online practice exams. This commitment ensures our customers always have access to the most current and accurate questions. By preparing with these actual questions, our customers can successfully pass the Fortinet NSE 5 - FortiAnalyzer 7.0 exam on their first attempt without needing additional materials or study guides.
Other certification materials providers often include outdated or removed questions by Fortinet in their Fortinet NSE5_FAZ-7.0 exam. These outdated questions lead to customers failing their Fortinet NSE 5 - FortiAnalyzer 7.0 exam. In contrast, we ensure our questions bank includes only precise and up-to-date questions, guaranteeing their presence in your actual exam. Our main priority is your success in the Fortinet NSE5_FAZ-7.0 exam, not profiting from selling obsolete exam questions in PDF or Online Practice Test.
For proper log correlation between the logging devices and FortiAnalyzer, FortiAnalyzer and all registered
devices should:
Refer to the exhibit.
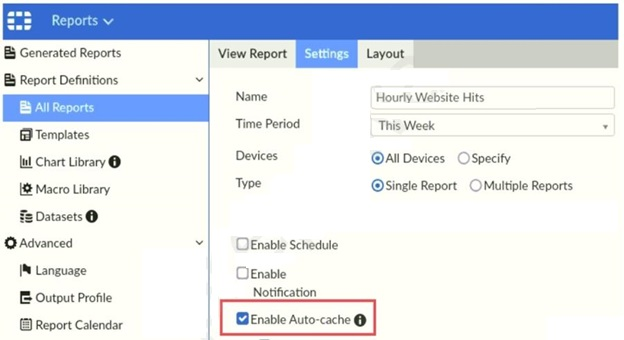
Which two statements are true regarding enabling auto-cache on FortiAnalyzer? (Choose two.)
'Enable auto-cache in the report settings to boost the reporting performance and reduce report generation time. Scheduled reports have auto-cache enabled already.'
FortiAnalyzer_7.0_Study_Guide-Online page 306